When
you enable Storage I/O Control on a datastore, ESXi host starts to
monitor the device latency that hosts observe when communicating with
that datastore. When device latency exceeds a threshold, the datastore
is considered to be congested and each VM that accesses that datastore
is allocated I/O resources in proportion to their shares. (by default
all VMs are set to Normal (1000) You set shares per VMDK. You can adjust
the number for each based on need. The default is 1000
01. Enable/Disable Storage I/O Control
02. Configure/Manage Storage I/O Control
03. Monitor Storage I/O Control
Enable/Disable Storage I/O Control:
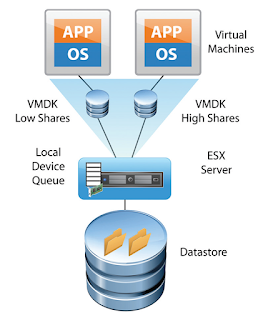
Before
we jump in I'd like to explain how storage I/O control helps to
prioritize certain VMs over the others. I think it's best to check out
this image from VMware which shows basically that after activating the
SIOC on shared datastore and setting up the shares (at the VMDK level)
on the VMs properties, the SIOC is able to prioritize those VMs over the
others.
Quote from VMware:
Storage
I/O Control operates as a "datastore-wide disk scheduler." Once Storage
I/O Control has been enabled for a specific datastore, it will monitor
that datastore, summing up the disk shares for each of the VMDK files on
it. Storage I/O Control will then calculate the I/O slot entitlement
per ESXi host based on the percentage of shares virtual machines running
on that host have relative to the total shares for all hosts accessing
that datastore.
Few limitations and requirements:
• NFS v4.1 isn't supported (it is for NFS v3).
• Storage I/O Control does not support datastores with multiple extents.
• SAN with auto-tiering has to be certified for SIOC.
• Datastores that are Storage I/O Control-enabled must be managed by a single vCenter Server system.
• Must be disabled before removing a datastore.
• Raw Device Mapping (RDM) is not supported. (it is on iSCSI NFS and FC).
• Activate at the datastore level via vSphere client or vSphere Web client.
Configure/Manage Storage I/O Control:
1. Enable Storage I/O Control for the datastore
In
the vSphere Client > select a datastore > Configuration tab >
Properties > Storage I/O Control, select the Enabled check box.
The advanced settings – Threshold – default value there. Check if the value is 30 ms.
2.
Set the number of storage I/O shares and upper limit of I/O operations
per second (IOPS) allowed for each virtual machine. Those settings at
the VMDK level so you could possibly prioritize disk where your
important production DB sits.
Set the threshold. More the VM is important, greater the number…… You can use the drop down or the custom and enter your value.
In case you're getting error on activating SIOC this can be due 2 reasons:
*
Not having proper licensing - “ Enterprise Plus is required. Storage
I/O Control (SIOC) requires Enterprise Plus licensing. Without this
license, the option to enable SIOC is grayed out.
* Check that the host is installed with ESXi 4.1 or higher.
Monitor Storage I/O Control:
There
is a Performance TAB to monitor Storage I/O. How Storage I/O Control
handles the I/O workloads of the virtual machines accessing a datastore
based on their shares.
Datastore performance charts allow monitoring:
* Average latency and aggregated IOPS on the datastore.
* Latency among hosts n Queue depth among hosts.
* Read/write IOPS among hosts.
* Read/write latency among virtual machine disks n Read/write IOPS among virtual machine disks.
From vSphere Web client > Datastore > Monitor tab > Performance tab > View drop-down menu > select Performance.
Want to download this blog as a PDF document, click the link below:
Abd El-Rahman Oreiby
Senior Data Center Engineer
Al Thuraya Security Egypt
www.abdelrahmanoreiby.weebly.com